Coverity Scan: wazuh/wazuh
| Project Name | wazuh/wazuh |
|---|---|
| Lines of code analyzed | 493,045 |
| On Coverity Scan since | Nov 30, 2016 |
| Last build analyzed | 8 days ago |
| Language | C/C++ |
| Repository URL | https://github.com/wazuh/wazuh.git |
| Homepage URL | https://github.com/wazuh/wazuh |
| License | GPL (GNU General Public License version ) |
Want to view defects or help fix defects?
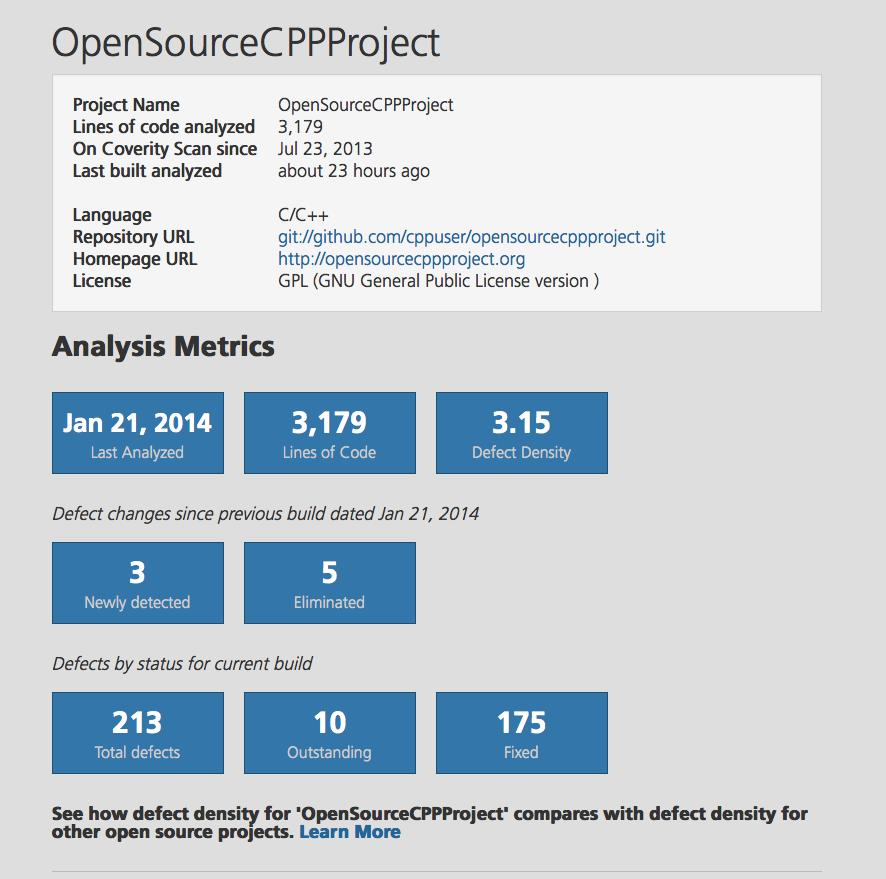
Add me to projectAnalysis Metrics
Version: 4.14.5-rc1
- Apr 17, 2026
- Last Analyzed
- 493,045
- Lines of Code Analyzed
- 227,078
- Lines of Code in Selected Components
- 0.92
- Defect Density
Defect changes since previous build dated Apr 13, 2026
- 0
- Newly detected
- 0
- Eliminated
Defects by status for current build
- 2,216
- Total defects
- 208
- Outstanding
- 1,846
- Fixed
See how defect density for 'wazuh/wazuh' compares with defect density for other open source projects. Learn more
Note: Defect density is measured by the number of defects per 1,000 lines of code.
Analysis Metrics per Components
| Component Name | Pattern | Ignore | Line of Code | Defect density |
|---|---|---|---|---|
| Active response | /active-response/.* | No | 0 | N/A |
| Agentless daemon | /agentlessd/.* | No | 0 | N/A |
| Analysis daemon | /analysisd/.* | No | 0 | N/A |
| Agent daemon | /client-agent/.* | No | 0 | N/A |
| Logcollector | /logcollector/.* | No | 0 | N/A |
| Monitord | /monitord/.* | No | 0 | N/A |
| Agent auth server and client | /os_auth/.* | No | 0 | N/A |
| Syslog client daemon | /os_csyslogd/.* | No | 0 | N/A |
| Database output daemon | /os_dbd/.* | No | 0 | N/A |
| Exec daemon | /os_execd/.* | No | 0 | N/A |
| Integrator daemon | /os_integrator/.* | No | 0 | N/A |
| Mailing daemon | /os_maild/.* | No | 0 | N/A |
| Remote daemon | /remoted/.* | No | 0 | N/A |
| Reporting daemon | /reportd/.* | No | 0 | N/A |
| Rootcheck | /rootcheck/.* | No | 0 | N/A |
| File integrity monitoring | /syscheckd/.* | No | 0 | N/A |
| Wazuh Database | /wazuh_db/.* | No | 0 | N/A |
| Wazuh Modules | /wazuh_modules/.* | No | 0 | N/A |
| Windows agent | /win32/.* | No | 0 | N/A |
| C++ Standard Library | /usr/include/.* | Yes | 128,678 | N/A |
| Analysisd | .*/analysisd/.* | No | 24,650 | 0.77 |
| External libraries | .*/external/.* | Yes | 137,289 | N/A |
| Other | .* | No | 202,428 | 0.93 |
CWE Top 25 defects
| ID | CWE-Name | Number of Defects |
|---|---|---|
| 22 | Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') | 3 |
| 190 | Integer Overflow or Wraparound | 21 |
Loading...
Loading...
Loading...
Loading...
Loading...
About Coverity Scan Static Analysis
Find and fix defects in your C/C++, Java, JavaScript or C# open source project for free.
Coverity Scan tests every line of code and potential execution path. The root cause of each defect is clearly explained, making it easy to fix bugs.